Today’s article is pretty straightforward, I’m going to show you how to show failed SSH login attempts. It should be a pretty short article, as I’m just going to show you two ways for a couple of system types. This is Linux, so there are certainly more ways to go about it, but I’ll show you a couple of them.
Yes, I’ve written about SSH a great deal. It is, in my opinion, one of the greatest remote administration tools ever conceived. But, attackers know this and any public-facing computer, with an IP address that can be reached externally, will be subject to port scanning and intrusion attempts.
I’ve written some SSH security articles, but one of the best things you can do is change the port that SSH uses. This will stop a bunch of malicious intrusion attempts. However, smart hackers will quickly scan for open ports with automated tools. Some of them will inevitably find your SSH port.
These people will then try to login. Securing your SSH is pretty important. I’ve written a few articles, so here’s a search of SSH-related articles previously published. Feel free to browse them at your leisure. I really need to do an article about Fail2Ban, but I haven’t gotten that far yet. One of these days!
So, like I said, you can show failed SSH login attempts. One of the things you can do with this information is scan for commonalities. You can also check to see if the hackers are using a username that already exists. If they’re using a username that already exists, it could be coincidental or it could mean they already have some insider information.
Well then, let’s jump into the article…
Show Failed SSH Login Attempts:
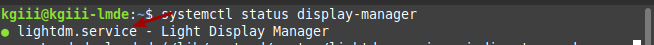
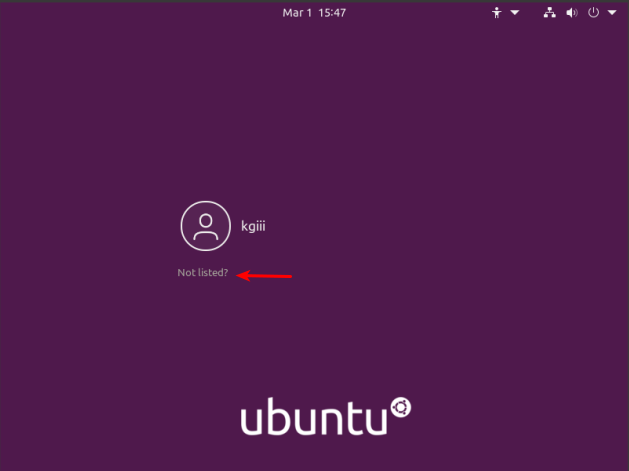
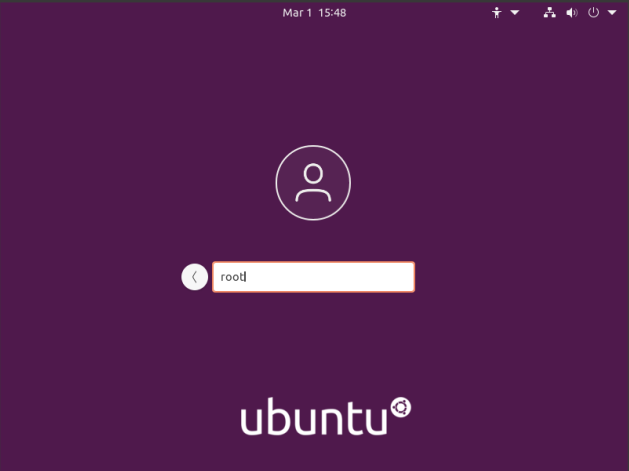
Like oh so many of my articles, and this one involving SSH, you’re going to want an open terminal for this. If you don’t know how to open the terminal, you can do so with your keyboard – just press
By the way, if you’re this far into the article and don’t know what SSH, it’s ‘secure shell’ and a way to remotely connect to another computer. Basically, you login to a remote computer and then you’re using the remote computer’s terminal. However, you can do so with graphics, you just need to forward x11.
So, it’s a pretty useful tool. I use SSH often, even in my own home. What? It’s faster than walking to another room, and I often test things remotely. SSH makes perfect sense for this sort of stuff.
With your terminal freshly open and properly logged into the remote computer, you can show failed SSH login attempts pretty easily. Like I said, I’ll show you a couple of ways. The first is pretty universal and should work with all but a couple distros:
1 | grep "Failed password" /var/log/auth.log |
RHEL and CentOS (Fedora too? I have not tested.) may store the data elsewhere, so you can try this command to show failed SSH login attempts:
1 | grep "Failed" /var/log/secure |
If you have failed SSH login attempts, one of those two commands should show you them. If the first doesn’t work, and you know you have failed attempts, try the second one. The logs are usually stored (as far as I know) in either of those two locations.
Closure:
See? It’s a nice and short article today, just like I said it would be. This time around, we’ve learned how to show failed SSH login attempts. Even if you’re using Fail2Ban and mandating certificate login, it’s always good to check to see what the bad guys are up to.
Thanks for reading! If you want to help, or if the site has helped you, you can donate, register to help, write an article, or buy inexpensive hosting to start your own site. If you scroll down, you can sign up for the newsletter, vote for the article, and comment.